Topics Archive

Cyber Security - Analyses & Assessments - Dec 21, 2017
Cyber Resilience
Sir David Omand, former Director of the Government Communications Headquarters (GCHQ), provided his predictions on how the cyber world will evolve and change over..
Cyber Security - Analyses & Assessments - Dec 20, 2017
Offensive Cyber
To assure their own cybersecurity, states will sometimes intrude into the strategically important networks of other states and will threaten, often unintentionally, the security..

Cyber Security - Analyses & Assessments - Dec 12, 2017
Changing paradigms in internal security
Since the advent of independence, India has faced a multitude of security challenges to its nationhood – both internal and external. A panel of experts at the Synergia..

Cyber Security - Analyses & Assessments - Dec 12, 2017
Financial and cyber terrorism
Global finance’s exclusive reliance on electronic communication, together with the billions of dollars traded daily, present lucrative opportunities to cyber-terrorists and criminals..
Cyber Security - Analyses & Assessments - Jun 28, 2017
Cyber threats: Who cares & Who should I call
The Synergia Foundation along with the Government of Karnataka hosted a round table on ‘Cyber threat- ‘Who cares & Who should I call?’? on 28 June 2017..

Cyber Security - Analyses & Assessments - Jun 20, 2017
Cyber Security: A Board Dilemma
Tobby Simon, the president of Synergia Foundation has written a report on ‘ CyberSecurity- A Board Dilemma’. In his report, he has brought out aspects that members of the board needs to understand…

Cyber Security - Analyses & Assessments - Jun 2, 2017
China Maintains Censorship
The ‘WannaCry ransomware’ which happened on 12th May, 2017 has affected over 150 countries surfacing as a global attack. This has led many countries to review their nation’s policies with regard to…

Cyber Security - Analyses & Assessments - Jun 2, 2017
Russia Fights against cyber crimes
Wan naCry ransomware attack on computers worldwide on 12th May 2017, has raised the issue of cybercrimes as well as increased the pressure on governments across the globe to strengthen cyber security…

Cyber Security - Analyses & Assessments - May 11, 2017
New-Age Pirates of the Sea
The ever-expansive cyber space has paved way for multiple potholes for users- as of recently, for an uber-deluxe community of superyacht owners.

Cyber Security - Analyses & Assessments - May 3, 2017
Future of American Surveillance
Following Edwards Snowden’s 2013 exposition of the National Security Agency’s PRISM and UPSTREAM surveillance programs, the government passed the Freedom Act of 2015. With origins in Bush’s Patriot…

Cyber Security - Analyses & Assessments - Apr 24, 2017
USA incarcerates Russian Hacker
On the 22nd of April 2017, a Federal Judge in the United States handed out the longest ever sentence imposed in the United States for a hacking-related case.

Cyber Security - Analyses & Assessments - Apr 21, 2017
Open Internet and Canada
Canadian Radio-television and Telecommunications Commission (CRTC) recently ruled in favor of net neutrality which essentially requires all Internet Service Providers (ISPs) to treat their data..

Cyber Security - Analyses & Assessments - Apr 17, 2017
Siege on Bitcoin
On the 17th April 2017, Bitcoin reported it was under threat from a group formed under the banner of the “Large Bitcoin Collider’(LBC). The group aims to attack user’s wallets by directing..

Cyber Security - Analyses & Assessments - Mar 30, 2017
US Online privacy bill
On March 29th 2017, The U.S Senate and House of Representatives both voted to revoke regulations that would have made it mandatory for Internet Service Providers or ISP’s to get the consumer’s…

Cyber Security - Analyses & Assessments - Mar 16, 2017
Turkish hacks
On the 15th of March, 2017 Hundreds of high profile twitter accounts were hacked by Pro-Erdogan Turkish hackers. The accounts including Forbes, Amnesty International and UNICEF were plastered with…

Cyber Security - Analyses & Assessments - Mar 16, 2017
Cyber War I
Cyberattack was just the latest directed against the United States by WikiLeaks last week: the release of an enormous cache of documents stolen from the Central Intelligence Agency. To visit the…

Cyber Security - Featured Article - Aug 20, 2019
Deep fake and targeted communication
Cybersecurity companies and scientists at the Defense Advanced Research Projects Agency (DARPA) are exploring ways to combat the threats posed by AI-enabled deep fake technology to the US election…
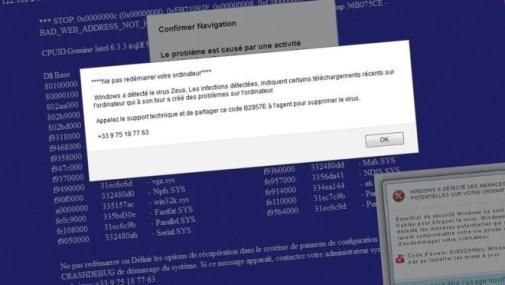
Cyber Security - Op-Eds - Nov 8, 2016
Blogger turns tables on cyber-scammer
A French security researcher says he managed to turn the tables on a cyber-scammer by sending him malware.

Cyber Security - Featured Article - Sep 30, 2019
Quantum Computing- Race to the Edge
While Moore’s Law or the exponential growth of integrated circuits refers to the fifth paradigm of computation, Quantum Computers may well be the sixth paradigm, given that they work in a fashion…

Cyber Security - Analyses & Assessments - Oct 20, 2020
Thought Capturing through Influence Operations
Cyberspace has opened a gateway for adversaries to disrupt democratic processes and weaken liberal democracies