Financial and cyber terrorism
November 24, 2017 | Expert Insights
Global finance’s exclusive reliance on electronic communication, together with billions of dollars of traded daily, present lucrative opportunities to cyber-terrorists and criminals from both within and outside the finance industry. How can large organizations as well as governments prevent such attacks from taking place?
The panel titled “Financial and Cyber Terrorism,” during The Synergia Conclave 2017 – Security 360, discussed these pertinent matters with inputs from experts. The panelists were Jean-Louis Brugine, former judge, Anti-Terrorism Court, Rajan Katoch, former Director, Enforcement Directorate, India and Frederick Douzet, Castex-Chair of Cyberstrategy, Institute of National Defense Studies, Paris.
Background
As the dependency on the internet increases from phones to hospitals and even cities, so do the threats posed by cyber terrorism. It is the use of the internet to conduct violent acts that result in, or threaten, the loss of life or significant harm, in order to achieve political gains through intimidation. It is also sometimes considered an act of Internet terrorism when activities, including acts of deliberate, large-scale disruption of computer networks, especially of personal computers attached to the Internet, through tools such as computer viruses, computer worms, phishing, and other malicious software and hardware methods and programming scripts are carried out.
The term “cyber terrorism” was first coined by Barry C. Collin of the Institute for Security and Intelligence in the late 1980’s, but the concept only began to resonate with the general public since the dawn of the new Millennium.
Analysis
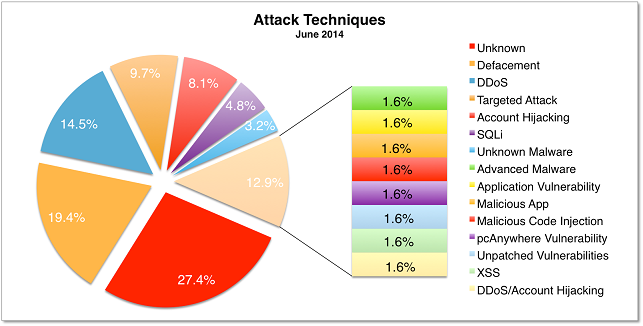
Frederick Douzet shared her thoughts on cyber enabled terrorism - the idea of using cyber infrastructure to launch major attacks on other infrastructures with malicious intent. There is a lot of talk and fear about this happening, but so far, we have not had any evidence that this has been done. Another interesting thing that has been evident in cyber-attacks is that a lot of attacks are being done as a strategic threat or intimidation, which does not target critical infrastructures, but target private companies with big consequences. Douzet highlighted that there is a high possibility that this kind of attack could be copied more. Apart from all this, she stressed that what we should be worried about even more, is the issue of the proliferation of cyber arms. The more arms there are out there, the more they can be re-engineered and reused, stolen and released – and the more access and entry ways would be open for terrorist. There is also the risk that these could be used for a targeted attack, she said.
She touched upon the problem of tracing and gathering evidence of cyber-attack related communications, since the platforms used are not national platforms – and countries have absolutely no authority in these spaces. This requires the right collaboration with the platforms that are being used by the terrorists. She warned that terrorist organizations had loopholes to hide in the legal internet, and hide in dark corners as well, creating situations where the fingers would be pointing at the platforms they use. Therefore, collaborations with social media platforms are essential for governments. For identifying and getting to the perpetrators, and because they often have the resources that governments lack. The larger solution requires a comprehensive strategic approach she remarked, which should not forget to take into account everything else that’s offline too.
Jean Louise Bruguiere opined that because we are talking about billions of dollars, it is important to formulate and create a very highly functional business model- looking at what is put in place and how the money is spent. He spoke about the situation with ISIS in terms of strategy, use of resources, and so on; money is the driving force behind being organized in this fashion. If you don’t have money you cannot run an organization like this. Now, since borders do not exist in the traditional sense, he remarked that it is getting very difficult to follow the money trail in terrorist organizations. He spoke about how we now have two sources that are compounding the problem – complicit sources and illicit sources. He emphasized that it is now easier for the terrorist organization to collect and transfer their funds to several countries, owing to the transactions being digital. Some terrorist groups were even using cyber frauds to create funding for themselves.
Rajan Katoch described the ‘downstream’ of what the main subject of the Conclave is –cybercrime. After a cybercrime is committed and money has been generated unfairly, it would be the job of the Enforcement Directorate to investigate where it actually went. Citing the examples of the recent digital bank heist in Bangladesh as part of the activities of international money laundering investigations, he went on to say many agencies and governments were working together on this. He pointed out that major businesses who were concerned about protecting themselves need an anti-cyber-attack wing for themselves. It important to be prepared, he said, and the direction given is that we should assume there is a hostile user who has the ability to access a system. Therefore, one thinks always about how to limit the damage that can be inflicted. He touched upon the need for government response – that we need an overarching decision-making structure which has its autonomy; a direction that he felt India is already moving towards. He also spoke about the need to reach out and seek the help of the private sector to ensure a better system to tackle evolving cybercrimes.
Assessment
Our assessment is that cybercrimes have no boundaries. Political, psychological and economic forces have combined to promote the fear of cyberterrorism. In the world of cyberspace, it is easy to figure out the weakness and vulnerabilities of the potential targets by the cyber terrorist.







Comments