Future of Cloud: Risks, Security and Governance
June 25, 2021 | Expert Insights

India is fast emerging as a leading digital power with a fair amount of sophistication, thus making it imperative for Indian experts to engage with their foreign counterparts to shape cloud security. India also happens to be a governance innovator and a huge marketplace for digital services.
UNDERSTANDING CLOUD
The wide range of characteristics peculiar to the cloud must be fully comprehended before a deeper look is taken into its security environment. The cloud represents a critical part of digital transformation, with its benefits being used universally by individuals, enterprises, and governments. Since there is a wide dependency on cloud services for both essential and non-essential services, its growth and evolution are taking place at a rapid pace. The pandemic has only contributed to this acceleration.
The cloud industry is mostly driven by the private sector, although in some countries, like India, it is the government that provides the requisite impetus as there are huge benefits in terms of security, growth, innovation, and efficiency. A worrying trait of the cloud is that today the infrastructure is largely concentrated in the hands of a few hyper-scale cloud service providers (CSPs) who are positioned beyond national borders. To tackle this concern, a global solution is necessary.
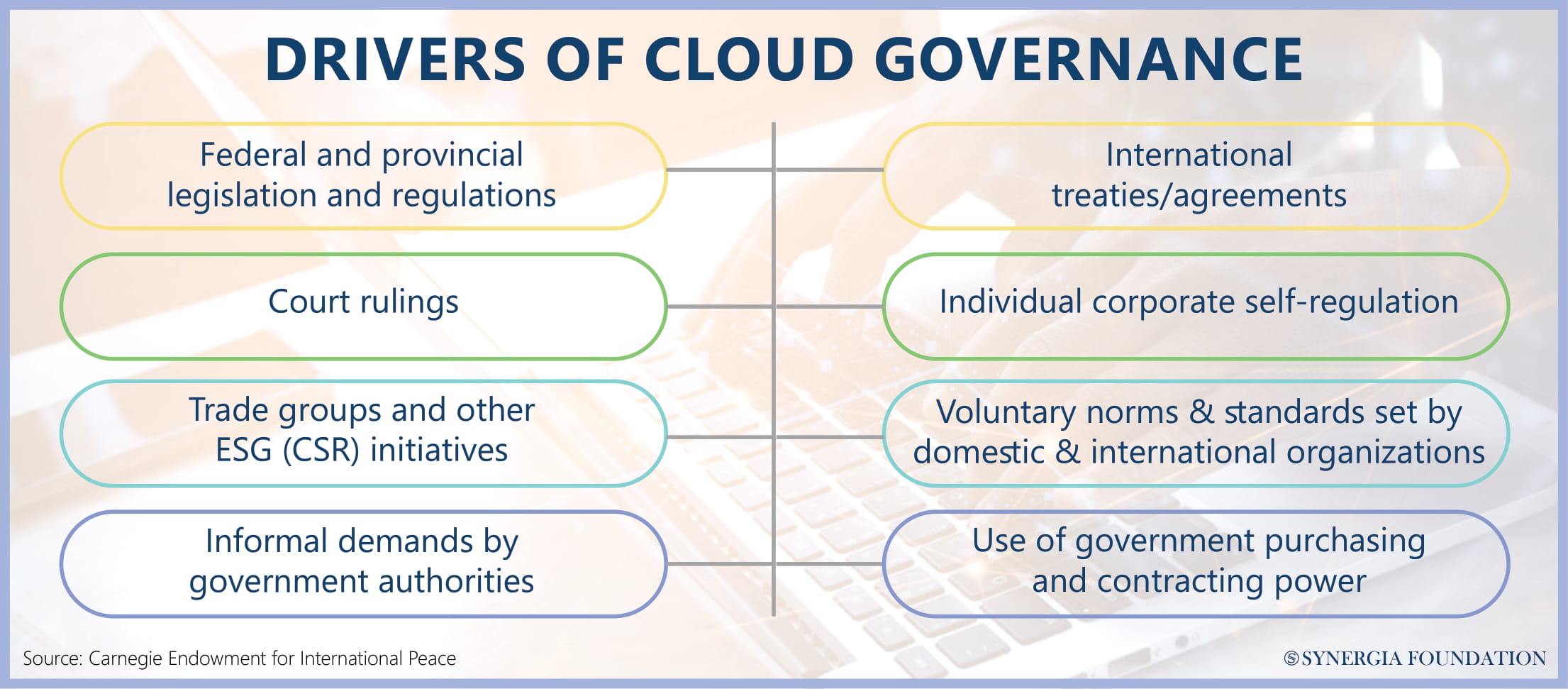
GOVERNANCE RISKS
The governance challenges in a cloud environment include direct risks such as severe disruptions in cloud services, either malicious (cyber-attacks) or non-malicious (natural disasters) or indirect risks rooted in dislocation and adjustments made in response to cloud dependency and bundling of services. Another critical challenge is to develop a global regulatory framework without stifling innovation.
This framework should be able to reduce the opaqueness caused by the complexity of the cloud, which makes risk modelling challenging, as also reduce the CSP oligopoly where one is overly dependent on a few providers. Most importantly, the regulations must devise a comprehensive responsibility framework to deal with both security and resilience to potential risks and attacks.
FIVE BASKETS OF GOOD GOVERNANCE
The governance issues can best be understood in five ‘baskets’ which will allow understanding through an organisational logic of delineating the key issues involved.
1) Security and Robustness: This represents the need to safeguard against both malicious and non- malicious triggers. This coupling will seem like a heavy proposition due to various government mandates, geographic and national locations. Cloud security goes much beyond traditional ideas of cybersecurity and is closely tied to various other non-malicious variables. This would mean developing a responsibility matrix and regulatory oversight, coordinating response effectively against incidents, sharing information and inter-governmental intelligence, moderation of cloud misuse, facilitating localisation requirements and cross-border data transfer arrangements etc.
2) Resilience: This is the ability to recover from mainly non-malicious triggers through maintaining data retrievability and back-ups, facilitating portability, interoperability, and multi-cloud arrangements. There must be a degree of assurance that the government steps in and takes over in case of extremities, ensuring provider and insurance carrier solvency and by investigating significant security breaches.
3) Consumer Protection: This basket deals with issues that flow from the power asymmetry between the providers of cloud services and the consumers. It also considers the dynamics when the government is also a consumer of these services. This should be done by preventing bias against consumers in services and application, informing and rewarding users for utilisation of their data, offsetting CSP market concentration and by informing the users of compromises made and thereby working to redress these compromises.
4) Prosperity and Sustainability: The challenges that the cloud can have on national well-being and development can be mitigated by the government. The state has a major role to play by supporting the development, dissemination, and operation of cloud infrastructure. It can promote its growth by extending its services via the cloud, establishing widespread broadband access and creating strict environmental standards on energy efficiency and emissions.
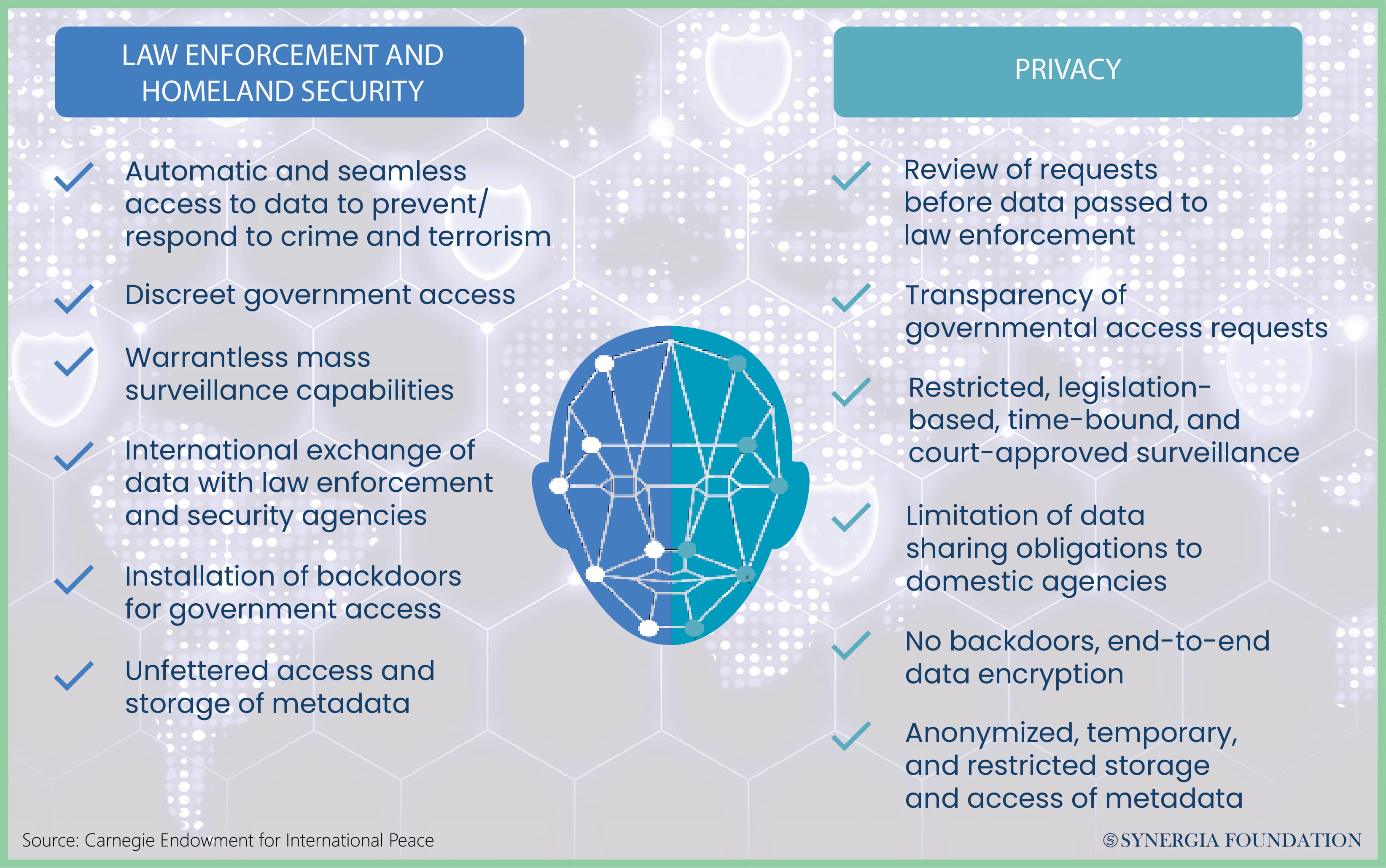
5) Human and Civil rights: The cloud hosts a large amount of private and sensitive data of its users as well as various essential services. To protect these assets, the access to cloud databases containing citizen’s identity and vital information should be restricted. As a human right concern, equitable access to the cloud must be mandated while concurrently, cloud services must be curtailed to known human rights abusers. These baskets are designed to identify key stakeholders’ perspectives, expose the deficiency in current arrangements as well as the possible incongruities in the various stakeholder perspectives.
All of them intertwine at various points to illustrate concepts like digital sovereignty and how content moderation overlap and entangle, making it necessary that we develop integrated and holistic approaches to cloud security.
GOVERNANCE TEMPLATES
The Integrated Responsibility Model aims to develop an integrated approach to adjudicate responsibility for cloud security, robustness and resilience between providers, consumers and governments across all sectors and functions. The prominent challenges this model aims to overcome are the various disagreements between stakeholders on how to share responsibility, the dynamics of the government being both a consumer and provider of cloud or cloud- based services, the mandates and jurisdictional limits which deter trans-national problem-solving mechanisms and the variations in the characteristics of the cloud services and models which hinder uniform solutions.
There is no clear separation in the division of labour and responsibility, which makes developing and maintaining systems of trust difficult. This model has been developed on the information collected from the survey on the shared responsibility model made available by cloud providers and cloud-based service providers, as well as from the deductions made by the Carnegie Foundation.
The role of governments (including government services such as certification), providers and customers overlap. The responsibilities shared by all are mainly taking steps to manage cyber risks and responding to incidents that threaten security. The responsibilities shared by providers and consumers include complying with norms and standards, facilitating recovery of data and security if compromised, changing management if necessary, as well as identity and access management. The customer-only responsibilities are relatively less when compared to providers and governments.
It is mainly to manage their data efficiently and to properly understand third-party dependencies. The provider- only responsibility is to protect cloud products, be it the physical infrastructure, network, or hard/ software. The government’s only responsibilities are mainly ensuring international norm-setting, certification, law enforcement, ensuring equitable access to cloud services and intelligence sharing.
The second governance template is to understand the anxieties arising with Cloud Security being deemed Critical Infrastructure (CI). As the world is growing dependant on cloud and cloud-based services, several governments have started thinking about designating cloud security as a critical infrastructure. The challenges here are mainly to understand risk prioritisation, raising many pertinent questions.
What is vital enough to be CI certified? How does one disaggregate between the cloud services and functions? Will this CI certification effectively give the government excessive control over the cloud? Would excessive certification and red taping of the cloud as different entities stifle innovation? The designation of cloud as CI can only be looked at holistically in intersection with other policy issues such as consumer protection, resilience, prosperity and sustainability and human rights.
DELINEATION OF RESPONSIBILITY
Therefore, the new regulatory approach is to leave it to the providers and make the government establish performance-based requirements. The government should define and segment high-level surety requirements along three main tangents, which are confidentiality, the type of services offered and sectorial criticality. The providers, in turn, should commit to honour them, educate the customers on their responsibility, develop an internal system of auditing, provide transparency and so on.
The providers can be given incentives to comply, such as insurance coverage, operational licenses etc. In parallel to cloud governance, there should be a process to understand cloud risk management. Cloud risk management can be undertaken by enhancing the understanding of cloud risks and modelling their consequences through an identification of the critical chokepoints that risk security.
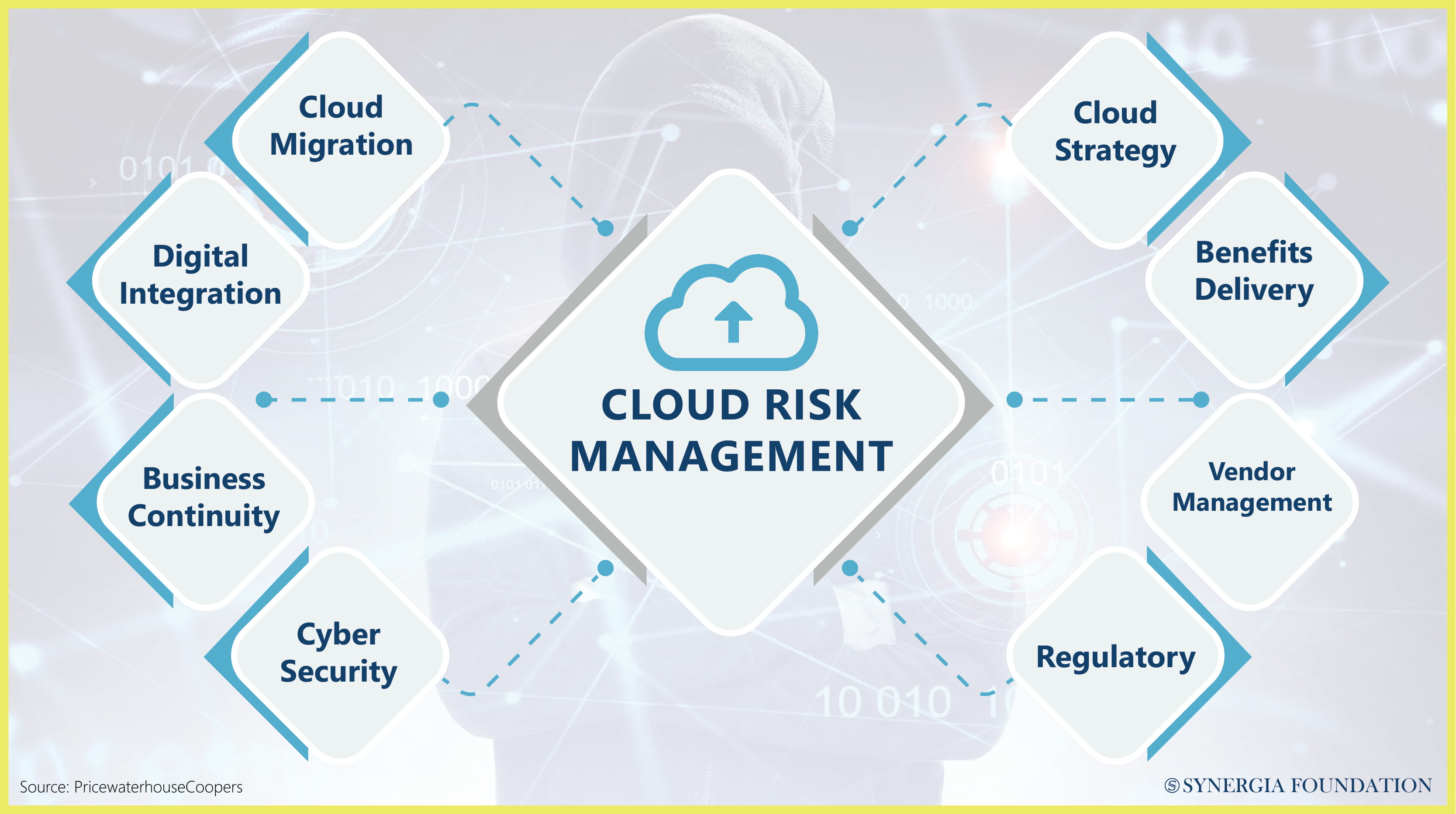
It is then imperative to diminish the probability of their occurrence and develop a proper responsibility matrix. The prime factor in promoting risk management efforts is to develop a working formula for government and private sector burden-sharing in risk channelling and management. Even high-scale private companies will find it hard to deal with large-scale security attacks if not backed by the government and its resources.
Ariel (Eli) Levite, is a non- resident Senior Fellow at the Nuclear Policy Program and Cyber Policy Initiative at the Carnegie Endowment for International Peace (CEIP). He is former Deputy Israeli National Security Advisor for Defense Policy, and also former Head of the Bureau of International Security and Arms Control, Ministry of Defense, Israel. Monica Pellerano is a research analyst at CEIP. This article is based on the presentation given by them at the 103rd Synergia Forum on the ‘Future of Cloud Security’.







Comments