Leveraging the Cloud
June 25, 2021 | Expert Insights

It is important to examine how the cloud can be leveraged to enhance security in sectors like critical infrastructure. This is an important issue, not just from a security point of view, but also from an operational resiliency perspective. Is it possible for critical services like energy or water to derive benefits from a ‘global commons’ like the cloud?
Irrespective of the nature of critical services or industries, the possibility of arriving at a common security baseline must be explored. Standards like the ISO may serve as valuable inputs in this regard. Once this has been achieved, the nuances can subsequently be worked out.
In any case, the fact that critical entities and infrastructure are undergoing digital transformation is a positive trend. Against this backdrop, the enhancement and encouraging of cloud services will only add further value to this exercise.
TRANSPARENCY AND VISIBILITY
As critical sectors migrate to the cloud, it is important to identify and assess the interests of policymakers and regulators. Most of them place emphasis on the norms of transparency and visibility, as they wish to be reassured about the security of cloud infrastructures. Apart from scrutinising the security practices and policies that a cloud provider affords to critical infrastructure, they seek to obtain guarantees on the management of resiliency capabilities. Most large-scale services, platform infrastructure and hyper-scale providers on the cloud inherit their security and resiliency requirements from customers and clients.
In this context, it might be useful to evaluate whether there are any commonalities across different sectors, which form an overarching umbrella for cloud service providers. Alternately, it must be examined whether it is easier to designate or apply specific standards for individual cloud providers.
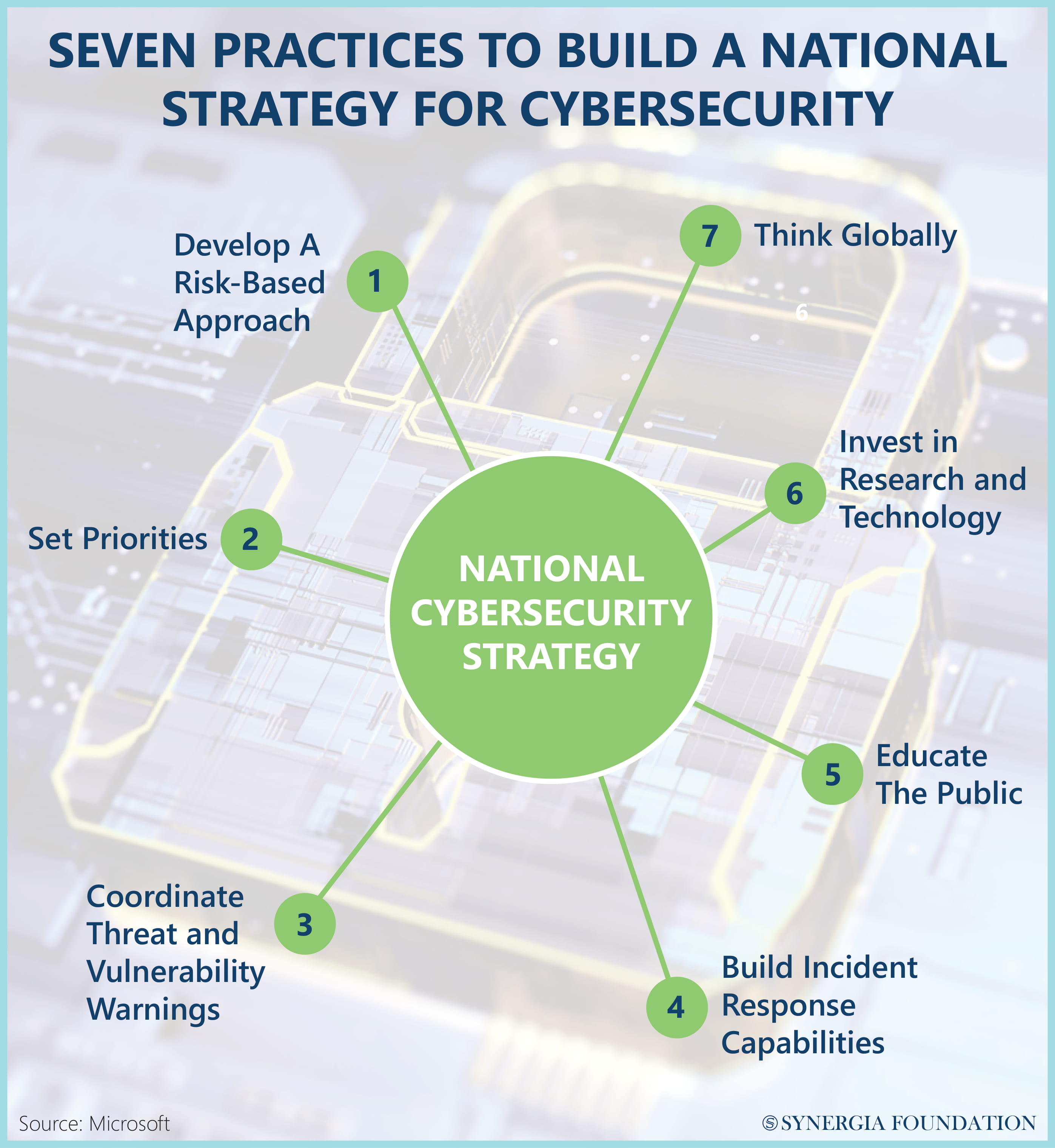
RISK-BASED APPROACH
Ultimately, these questions need to be assessed through a risk-based lens. It is important to identify critical
services and then apply risk-based assessments to these sectors. Based on the outcomes, one can assess the specific areas that need additional resources or efforts.
Governments and policymakers can play a crucial role in tracking the risk exposure across different critical sectors. As most industries transition to the cloud, it is important to have a risk-based, cross-sectoral view that foresees a spill-over of threats into vital entities. In grappling with these interconnected problems, the importance of public- private partnerships should not be underestimated. The tapping and harnessing of talent in cyber security should also be encouraged. For a company such as Microsoft, it is exceedingly critical to foster talent pools across the world.
Chelsea Smethurst, is a Senior Security Strategist at Microsoft.







Comments