An All-Pervasive Presence
June 25, 2021 | Expert Insights
Facilitating conversations on the future of cloud security is exceedingly important. As of today, there is growing awareness of the vital role played by this industry in critical infrastructure as well as businesses. Over the coming years, policy decisions and actions will be driven by better risk sentience.
CRITICAL INFRASTRUCTURE
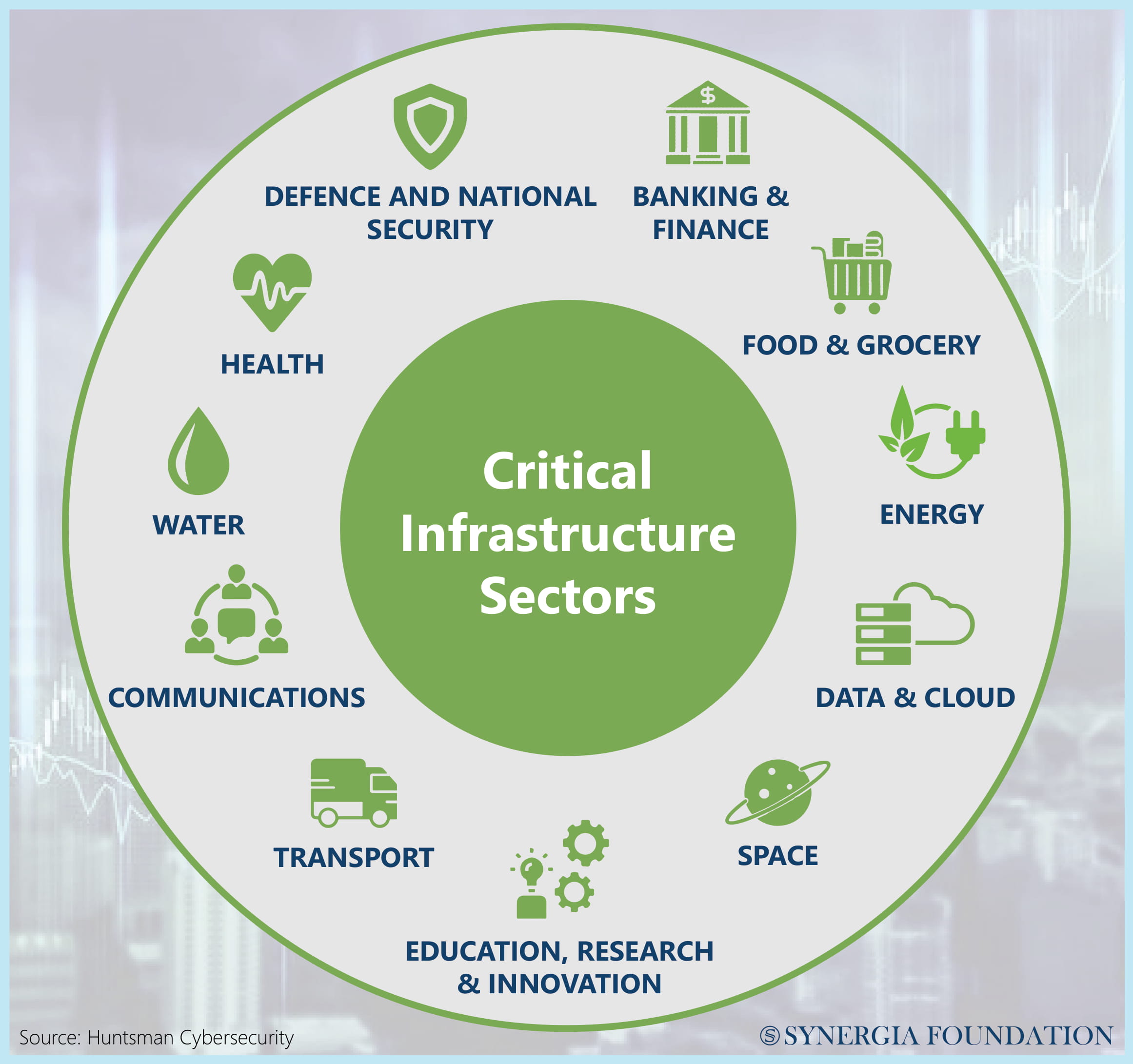
While identifying cloud services and platforms that qualify as critical infrastructure, it is important not to cast the net too wide. Many jurisdictions like Australia, India and the U.S. have similar definitions of critical infrastructure that seek to address any disruption to societal well-being, national security, or the ordinary lives of citizens. Such nuanced characterisations are essential to prevent every cloud application from being designated operations. Therefore, it is possible to trace an element of criticality in the cloud environment from its foundational source.
RISK ACCOUNTING
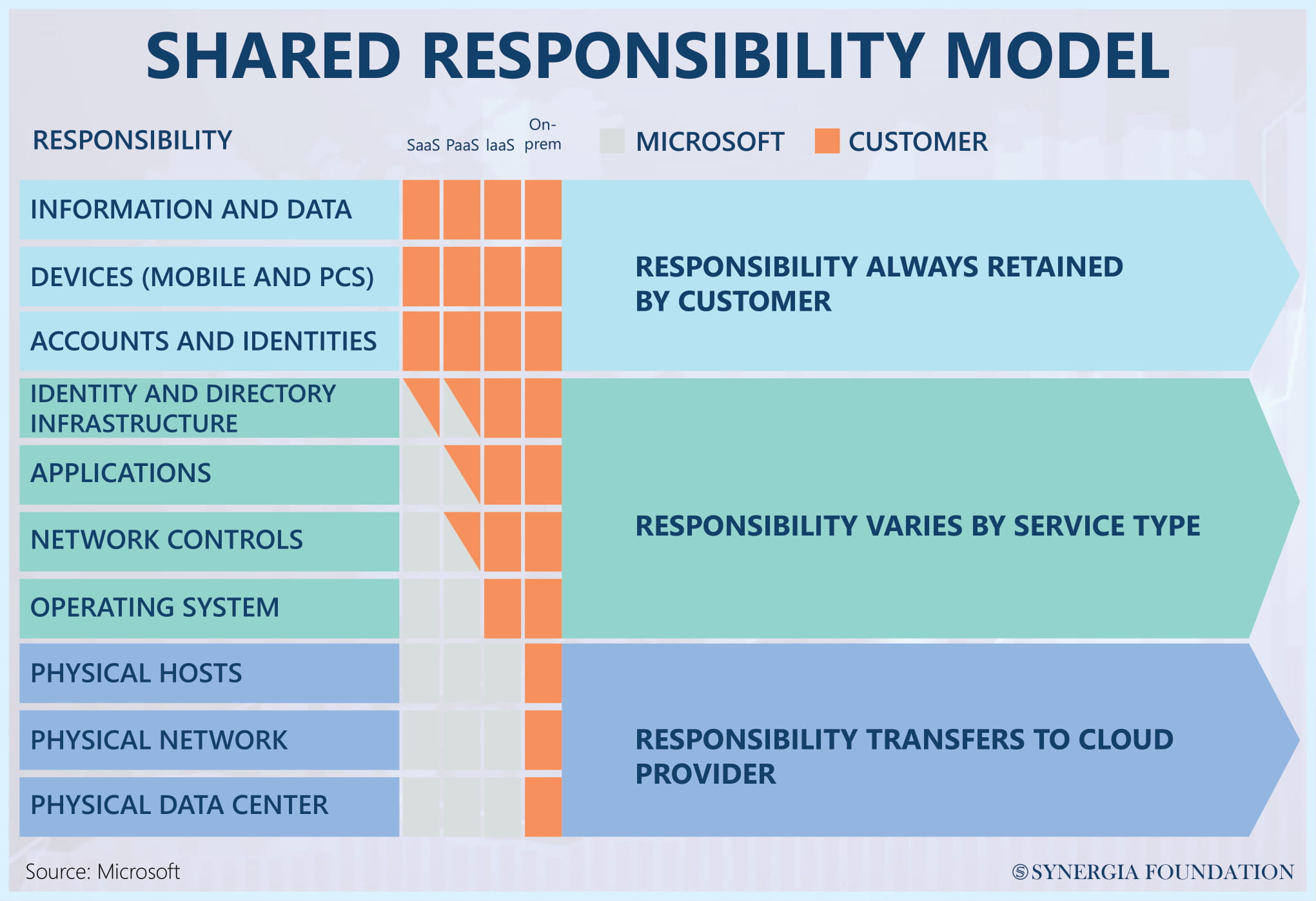
On comparing the cloud to private data centres, it could be argued that the technology stack is largely consistent. Both have elements of storage, networking, and computer applications. What is different, however, is their emphasis on models of shared responsibility. Irrespective of whether one is running the cloud, consuming the cloud, or engaging in ‘on-premises’ IT, the cloud system provides for better accountability on the part of every stakeholder. The responsibility to treat risks is not solely vested in the service provider. By highlighting the importance of identity and access control, it accords equal importance to responsibilities that reside with a consumer.
AVOIDING DUPLICATION
For cloud providers, the recognition of international standards, certifications and audits will be important for scaling up their security frameworks and satisfying the demands of governments and consumers. If every country devises a bespoke certification or security regime, many of them may tend to overlap. From a purely technical control perspective, such duplication of efforts needs to be avoided. For example, in Australia, lawmakers are currently in the process of updating the Critical Infrastructure Bill.
By virtue of this legislation, the number of critical infrastructure sectors is slated to increase from three to eleven. In this context, one of the primary challenges for cloud providers will be to ensure that eleven different regulators do not develop their own risk assessment frameworks. To avoid such duplication, it is important to evaluate the default native infrastructure of cloud providers against existing standards like ISO or SOC 2 audits.
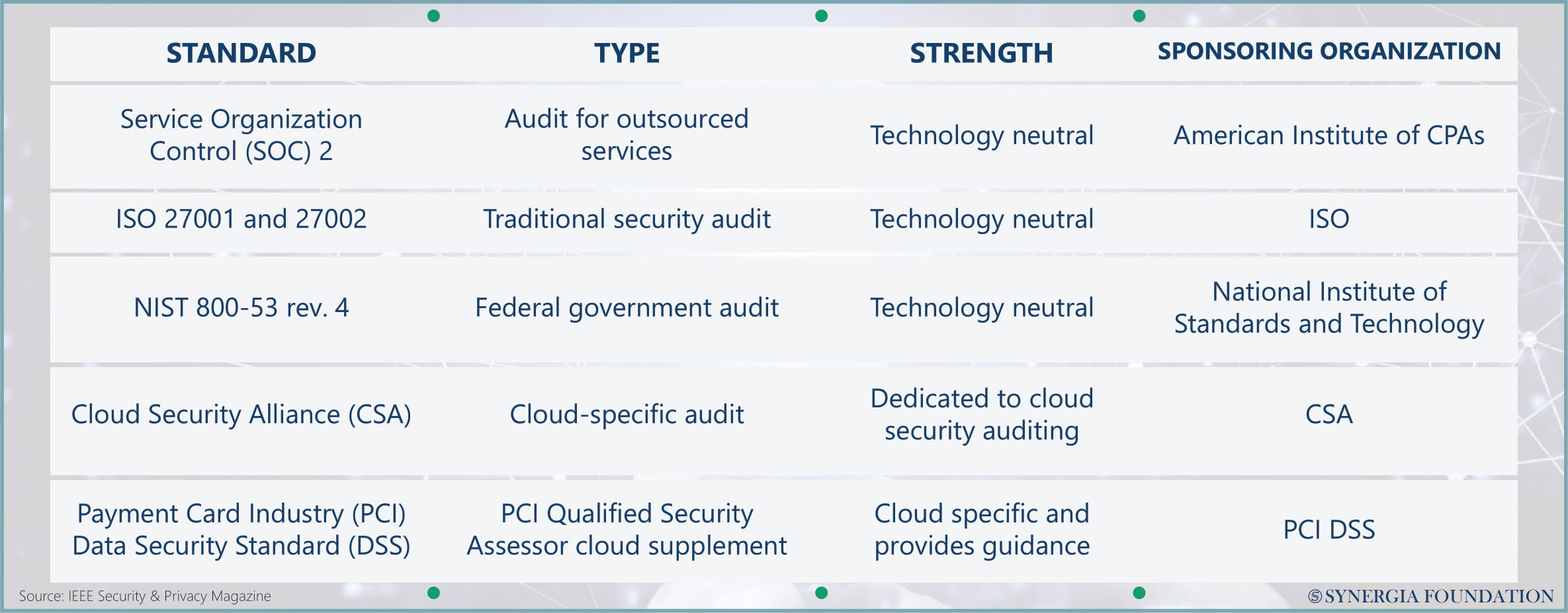
If governments and regulators can map the extent to which these frameworks have already addressed some of their security concerns, then future risk assessment protocols and security standards can be formulated accordingly. At the end of the day, however, the future of cloud security looks positive, with policy engines and infrastructure codes promising to place the industry in a better spot than before.
Matt Carling, is a Cyber Security Solutions Architect at Cisco Systems. This article is based on his views at the 103rd Synergia Forum on the ‘Future of Cloud Security’.







Comments